First of all, let me be a psychic for 5 seconds and tell you, “I know you’re using a pirated copy of Windows activated by some tool like KMSpico.”
How do I know?
Read the eighth word of this post.

Now that I have your attention with this fantastic God-tier meme, let me provide you with some intel regarding what this process is, if it is safe or malicious, and how to deal with it (I solemnly swear I am not going to tell you to “deal wit it”).
Intel
Intel 1: The process & its origin
The process ‘SppExtComObjHook.dll’ and some other files—most of them having the ‘Spp’ prefix—are all related to the Windows activating tool known as KMSpico. The files being referred to are shown below:
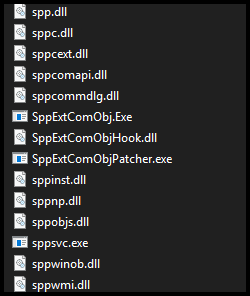
All these files are located in the System32 folder in Windows and the nature of these files are mostly unknown.
Intel 2: Safe or malicious?
Although various antivirus and antimalware applications detect the ‘SppExtComObjHook.dll’ file as malicious, it is completely harmless and malignant. At least up till now. It has not known to cause any issues or usage of system resources (CPU, RAM, etc.) as of yet. Just a few security applications have flagged the file as malicious but that is a mere false positive. You should know what that is by now, you filthy SKIDROW pirate.
But just in case, if this process is somewhat of a sleeper agent file and becomes sentient (w0ke.exe) some day, I will not be responsible for the chaos and rebellion it causes.
Just kidding, file’s safe. Quit being a pansy.
How To Still Remove It
You still do not feel safe with the process running all the time in your Task Manager, and you want it gone. All this while maintaining your pirated and activated copy of “genuine” Windows. Don’t worry, pirate. I’ve got you covered. I was in the same boat (get it? Pirate? Boat? Told you, memeg0d).
Step 1: Enable showing file extensions
In order to make this solution work, you will have to be able to read and edit file extensions. This can be done by pressing the Start key and typing in “Folder options”. The first result to likely be shown should be the Control Panel entry for either “Folder Options” or “File Explorer Options”, depending on which version of Windows you have.
Click on that result:

You should now have a Folder Options window appear. Go to the “View” tab and search for the “Hide extensions for known file types” option. Once you have found it, uncheck the box next to it, as shown below:

Done. You have enabled showing file extensions.
Step 2: Navigate to the .dll file
Go to your System32 directory, which is located in the Windows directory. Typically, this should be:
C:\Windows\System32
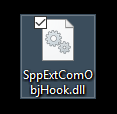
Now, scroll down until you reach the block of files which have the “Spp” prefix (assuming you have the files alphabetically arranged in ascending order). The file we need to focus upon due to our Task Manager issue, is SppExtComObjHook.dll, highlighted below:

Step 3: Dealing wit it
Now, you can obviously just delete this file and have no consequences. But just to be safe, let’s choose the safest approach to this issue. We will make a blank dummy file with the same name that is 100% harmless (since you’re making it, you’d be 100% sure) so that when it is executed and called upon by the KMSpico service, nothing really happens.
For this, first go to the Task Manager and end the SppExtComObjHook.dll process. This will allow us to make some changes in the further steps.
After doing so, go back to the System32 folder and rename the .dll file to have some other extension, any other extension, just so it is not able to execute. For example, I chose “.NOPE” as the extension:

We have made sure that Windows will not execute this process anymore automatically since it is not even a functional extension anymore.
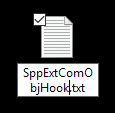
Now, just in case this process’s execution is in some way crucial to your copy of Windows being activated and “genuine”, we will make a dummy duplicate file. This can be done by creating a new text document. To do so, right-click in an empty area in the same folder, and select “New”, then “Text Document”. Like so:

This text document can be empty, or you can fill it with rainbows and unicorns or your dreams. It doesn’t matter. None of the things mentioned matter. All are the same as the first option—empty.

Next, rename this text file exactly as the .dll file that’s causing you insecurity issues—”SppExtComObjHook”:
Then, taking advantage of the extension setting we changed in step 1, change the “.txt” part to “.dll”, like so:
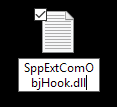
Push Enter. You will be shown a prompt asking if you really want to change the extension of the file:

Hit the “Hell Yeah” button. You will now have a decoy SppExtComObjHook.dll file that doesn’t do anything at all.
Done. You have rendered the original .dll file harmless completely even if it already was harmless in the first place, and for extra security, you even made a 100% harmless replacement of it that even if executed, won’t do anything at all.
Your sense of security should now be at level 9,000+, and if not, then welcome to the void.

That is informative. Thank you.
LikeLike
This was very informative, sir. Thank you.
LikeLike